[Helpful information related to the current article]
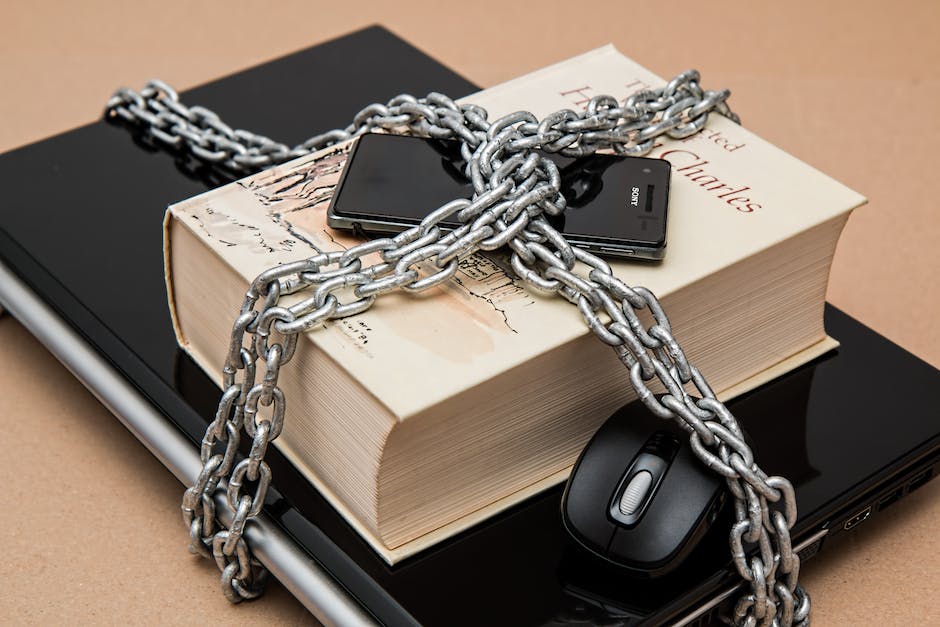
Are you concerned about the security of your digital assets? In today’s interconnected world, cyber threats are ever-present, making it crucial to have an efficient security policy in place. In this comprehensive guide, we will delve into the essential elements of crafting a robust cybersecurity strategy. We’ll explore the key components, practical tips, and best practices to safeguard your organization from potential breaches. Let’s find out exactly how to enhance your cybersecurity defenses and protect your valuable data. Let’s find out in detail in the article below. I’ll tell you exactly!
Introduction
The Importance of Cybersecurity
In today’s digital age, organizations of all sizes and industries rely heavily on technology and digital assets to carry out their day-to-day operations. However, this increased reliance on technology also brings along an increased risk of cyber threats. The consequences of a successful cyber attack can be devastating, resulting in data breaches, financial losses, damaged reputation, and regulatory non-compliance. Therefore, it is essential for organizations to prioritize cybersecurity and develop an efficient security policy to protect their valuable data and assets.
The Need for an Efficient Security Policy
Crafting a comprehensive security policy is crucial for organizations to establish guidelines and protocols for safeguarding their digital assets. An efficient security policy serves as a framework that outlines the organization’s security objectives, defines roles and responsibilities, and provides guidelines for implementing security measures. It sets the tone for the organization’s cybersecurity posture and ensures that all employees are aware of their responsibilities and the steps they need to take to protect the organization’s assets.
Key Components of a Security Policy
Risk Assessment and Management
A critical element of developing an efficient security policy is conducting a thorough risk assessment. This involves identifying and evaluating potential vulnerabilities and threats that could impact the organization’s digital assets. By understanding the risks, organizations can prioritize their security efforts and allocate resources effectively. Risk management strategies should be defined in the security policy, including measures such as regular vulnerability scans, penetration testing, and incident response plans.
Security Governance and Compliance
To ensure that cybersecurity is ingrained in the organization’s culture, a security governance framework should be established. This framework defines the roles and responsibilities of key personnel, such as the Chief Information Security Officer (CISO) or security team, and outlines the reporting structure for security-related matters. Moreover, the security policy should address compliance with applicable laws, regulations, and industry standards to ensure that the organization meets the necessary security requirements.
Access Control and User Management
Controlling access to digital assets is essential for maintaining data confidentiality and preventing unauthorized users from accessing sensitive information. The security policy should define access control mechanisms such as strong password policies, multi-factor authentication, and regular user access reviews. Additionally, user management processes, including onboarding and offboarding procedures, should be clearly documented to ensure that access privileges are granted or revoked appropriately.
Practical Tips for Implementing an Efficient Security Policy
Engage Leadership and Create Awareness
Engaging leadership from the beginning is crucial for the successful implementation of a security policy. It is important to gain their support, establish a security culture, and allocate the necessary resources to implement and maintain the policy effectively. Creating awareness among employees about cybersecurity best practices and the significance of the security policy will help foster a proactive security mindset throughout the organization.
Regular Training and Education
Investing in regular training and education programs for employees is essential to ensure they are equipped with the knowledge and skills to follow the security policy effectively. Training should cover topics such as phishing awareness, secure coding practices, and incident response procedures. By keeping employees up to date with the latest cybersecurity developments, organizations can enhance their overall security posture.
Continuous Monitoring and Evaluation
Implementing a security policy is not a one-time task; it requires continuous monitoring and evaluation to ensure its effectiveness. Regular security assessments, vulnerability scans, and penetration testing should be performed to identify any weaknesses or gaps in the security measures. Incident response drills and tabletop exercises can also be conducted to test the organization’s response capabilities. Based on the findings, the security policy should be reviewed and updated as necessary.
Best Practices in Cybersecurity
Regular Patching and Updates
Keeping all software and systems up to date with the latest patches and updates is critical to protect against known vulnerabilities. Regular patch management processes should be implemented to ensure that all devices, applications, and infrastructure are regularly updated with the latest security patches.
Implementing Defense-in-Depth
A defense-in-depth strategy involves layering multiple security measures to protect against various types of attacks. This can include network segmentation, firewalls, intrusion detection/prevention systems, antivirus software, and employee awareness training. By implementing multiple layers of security controls, organizations can significantly enhance their resistance against cyber threats.
Data Encryption and Backup
Encrypting sensitive data both at rest and in transit adds an extra layer of protection against unauthorized access. Additionally, regular backups of critical data should be performed and stored securely, preferably offsite. In the event of a security breach or data loss, having reliable backups ensures that the organization can quickly recover and resume normal operations.
Conclusion
Crafting an efficient security policy is a vital step in enhancing your organization’s cybersecurity defenses. By considering the key components discussed in this guide, you can develop a robust security strategy that protects your valuable digital assets from potential cyber threats. Remember to regularly review and update your security policy to adapt to the evolving threat landscape and ensure that your organization remains resilient against emerging cyber risks. Prioritize cybersecurity, engage leadership, and foster a security-conscious culture throughout your organization to create a strong defense against cyber threats.
Additional Information
1. Conduct regular security audits and assessments to identify potential vulnerabilities and areas for improvement.
2. Implement a robust incident response plan to effectively handle and mitigate the impact of security incidents.
3. Stay informed about the latest cybersecurity trends and keep up to date with emerging threats and vulnerabilities.
4. Establish strong partnerships with trusted cybersecurity vendors and experts for additional support and guidance.
5. Foster a culture of accountability and responsibility for cybersecurity throughout the organization, encouraging all employees to actively participate in protecting digital assets.
[Other information related to this article]
➡️ Unlocking the Power of AI-Powered Image Recognition: Revolutionizing Visual Data Analysis